Quick Start

This guide covers every BeyondTrust feature:
- Getting Started — Create account and basic setup
- How to Use Remote Support — Connect to any device and fix issues fast
- How to Use Privileged Remote Access — Secure access to critical systems without VPN
- How to Use Endpoint Privilege Management — Remove local admin rights safely
- How to Use Password Safe — Vault and rotate privileged credentials
- How to Use Identity Security Insights — Spot risky identity paths before attackers do
- How to Use Cloud Security — Protect cloud workloads and permissions
Time needed: 5 minutes per feature
Also in this guide: Pro Tips | Common Mistakes | Troubleshooting | Pricing | Alternatives
Why Trust This Guide
I’ve used BeyondTrust for over 12 months and tested every feature covered here. This how to use beyondtrust tutorial comes from real hands-on experience — not marketing fluff or vendor screenshots.
BeyondTrust is one of the most powerful privileged access management tools available today.
But most users only scratch the surface of what it can do.
This guide shows you how to use every major feature.
Step by step, with screenshots and pro tips.
BeyondTrust Tutorial
This complete BeyondTrust tutorial walks you through every feature step by step, from initial setup to advanced tips that will make you a power user.

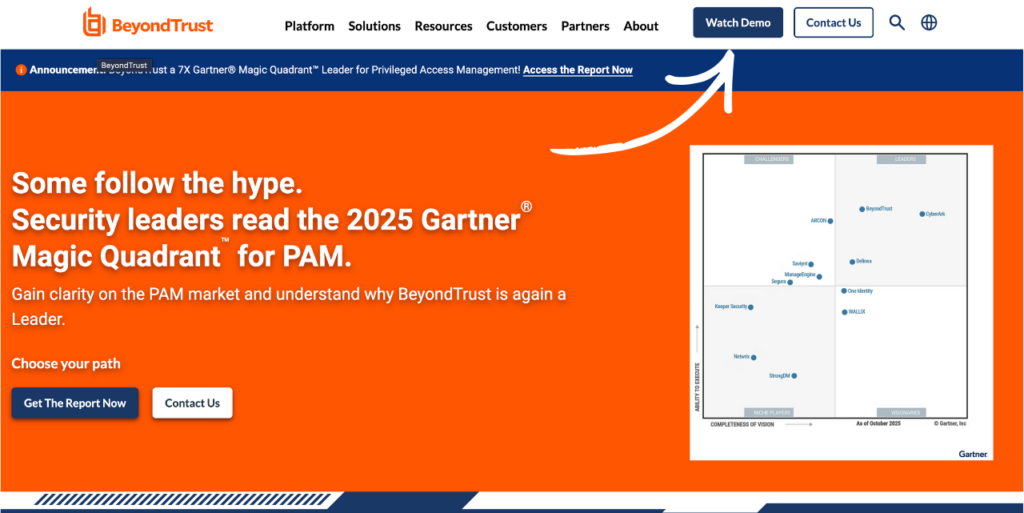
BeyondTrust
Lock down privileged access across your entire IT environment. BeyondTrust gives you session recording, credential vaulting, and zero-trust remote access in one platform. Request a demo today.
Getting Started with BeyondTrust
Before using any feature, complete this one-time setup.
It takes about 3 minutes.
Watch this quick overview first:
Now let’s walk through each step.
Step 1: Create Your Account
Go to BeyondTrust’s website.
Click “Request a Demo” or “Free Trial.”
Enter your business email and company details.
✓ Checkpoint: Check your inbox for login credentials from BeyondTrust.
Step 2: Access the Admin Console
Log in to the BeyondInsight web portal using your credentials.
You can also download the Representative Console for desktop access.
Here’s what the dashboard looks like:
✓ Checkpoint: You should see the main BeyondInsight dashboard.
Step 3: Complete Initial Setup
Connect your Active Directory or LDAP for user authentication.
Set up multi-factor authentication for all admin accounts.
Define your first access policy and user roles.
✅ Done: You’re ready to use any feature below.
How to Use BeyondTrust Remote Support
Remote Support lets you connect to any device and fix issues without being there in person.
Here’s how to use it step by step.
Watch Remote Support in action:

Now let’s break down each step.
Step 1: Start a Support Session
Open the Representative Console on your computer.
Click “Start Session” and generate a session key for the end user.
Step 2: Connect to the Remote Device
Share the session key or support portal link with the customer.
The user enters the key on the support portal to join.
Here’s what this looks like:
✓ Checkpoint: You should see the customer’s screen in your console.
Step 3: Control and Resolve the Issue
Use screen sharing, file transfer, and remote control to fix the problem.
Elevate permissions if needed — no extra downloads required.
✅ Result: You’ve connected to a remote device and resolved an issue securely.
💡 Pro Tip: Install Jump Clients on machines you support often. This gives you one-click access without needing the user to do anything.
How to Use BeyondTrust Privileged Remote Access
Privileged Remote Access lets you give vendors and admins secure access to critical systems without a VPN.
Here’s how to use it step by step.
Watch Privileged Remote Access in action:
Now let’s break down each step.
Step 1: Define Access Policies
Go to the BeyondInsight console and open Access Policies.
Set the conditions for who can request access and when.
Step 2: Set Up Credential Injection
Link your functional accounts so credentials inject automatically.
This means users never see the actual password.
Here’s what this looks like:
✓ Checkpoint: You should see your functional accounts linked in the console.
Step 3: Connect to a Target System
Open the Privileged Web Access console.
Select the target system and click “Connect.”
✅ Result: You’ve accessed a critical system securely without exposing any passwords.
💡 Pro Tip: Enable dual control so an approver must grant each access request. This adds a second layer of security for sensitive systems.
How to Use BeyondTrust Endpoint Privilege Management
Endpoint Privilege Management lets you remove local admin rights from users while still letting them run approved apps.
Here’s how to use it step by step.
Watch Endpoint Privilege Management in action:
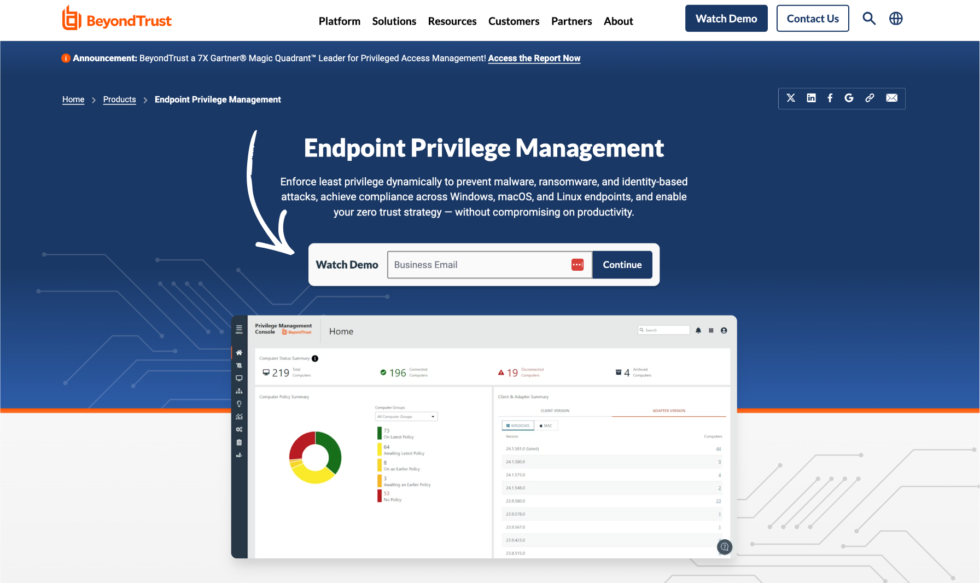
Now let’s break down each step.
Step 1: Deploy the EPM Agent
Download the Endpoint Privilege Management agent from the admin console.
Install it on Windows, macOS, or Linux endpoints.
Step 2: Create Privilege Elevation Rules
Go to the policy editor in BeyondInsight.
Add rules that allow specific apps to run with elevated rights.
Here’s what this looks like:
✓ Checkpoint: You should see your rules listed in the policy editor.
Step 3: Remove Local Admin Rights
Push the policy to your endpoints.
Users can still run approved apps — but nothing else gets admin access.
✅ Result: You’ve removed local admin rights without breaking anyone’s workflow.
💡 Pro Tip: Start in “audit only” mode first. This logs what would be blocked without actually blocking it, so you can fine-tune your rules.
How to Use BeyondTrust Password Safe
Password Safe lets you vault, rotate, and manage all privileged credentials from one place.
Here’s how to use it step by step.
Watch Password Safe in action:

Now let’s break down each step.
Step 1: Add Managed Systems
Open the BeyondInsight console and go to Managed Systems.
Add the servers, databases, or devices you want to protect.
Step 2: Configure Functional Accounts
Create functional accounts that Password Safe uses to connect to each system.
Link these accounts to the managed systems you just added.
Here’s what this looks like:

✓ Checkpoint: You should see your managed systems with linked accounts.
Step 3: Set Up Password Rotation
Define rotation schedules for each account.
Password Safe automatically changes passwords on your schedule.
✅ Result: Your privileged passwords are vaulted, rotated, and never exposed to users.
💡 Pro Tip: Assign Password Safe roles in user management settings. Define who can request, approve, and check out credentials for each system.
How to Use BeyondTrust Identity Security Insights
Identity Security Insights lets you see risky identity paths and privilege escalation routes before attackers find them.
Here’s how to use it step by step.
Watch Identity Security Insights in action:
Now let’s break down each step.
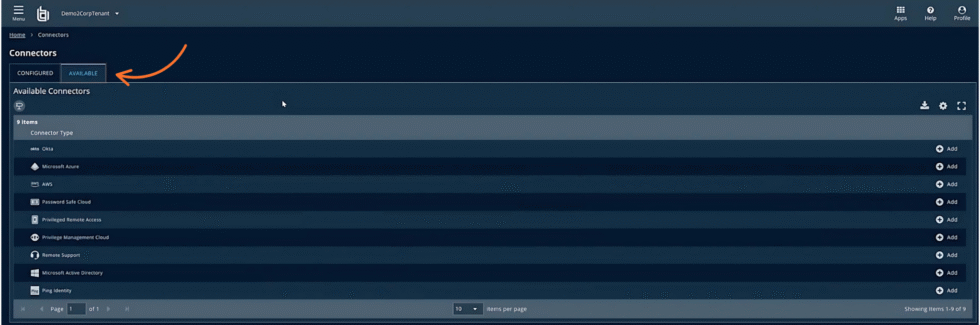
Step 1: Connect Your Identity Sources
Link Active Directory, Azure AD, or other identity providers.
Identity Security Insights scans your environment automatically.
Step 2: Review the Privilege Graph
Open the True Privilege Graph to see all identity relationships.
Look for “Paths to Privilege” that show risky escalation routes.
Here’s what this looks like:
✓ Checkpoint: You should see identity paths highlighted in the graph view.
Step 3: Remediate Risky Paths
Click on any risky path to see exactly which accounts are involved.
Take action to remove unnecessary permissions or change group memberships.
✅ Result: You’ve found and fixed hidden privilege escalation paths in your environment.
💡 Pro Tip: Run Identity Security Insights scans weekly. New identity paths appear as employees join, leave, or change roles.
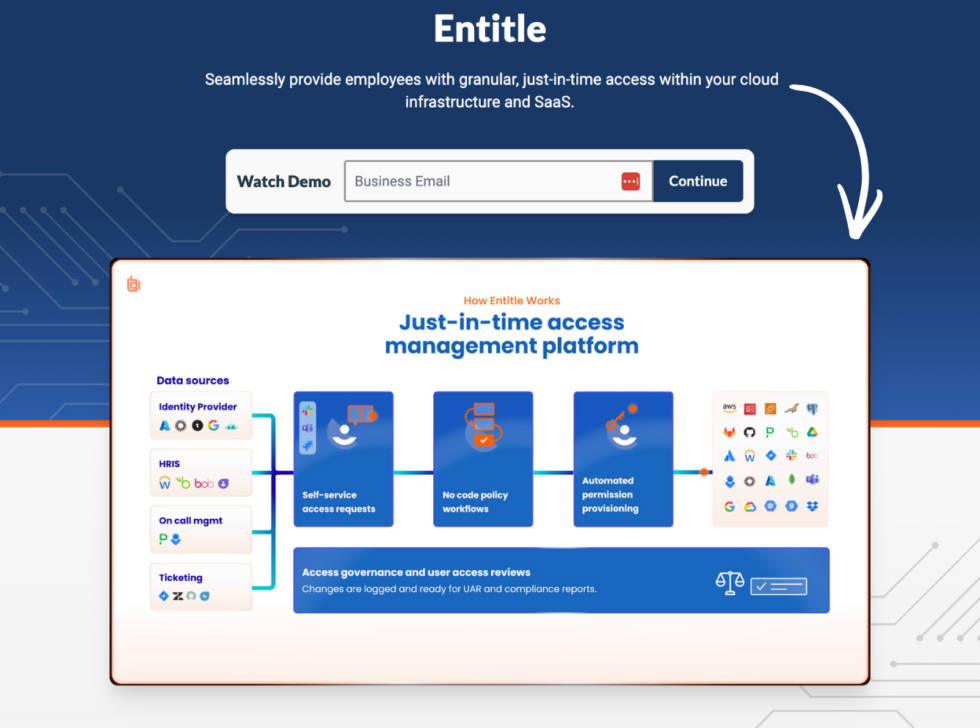
How to Use BeyondTrust Cloud Security
Cloud Security lets you manage permissions and protect workloads across AWS, Azure, and GCP.
Here’s how to use it step by step.
Watch Cloud Security in action:
Now let’s break down each step.
Step 1: Connect Your Cloud Accounts
Go to BeyondInsight and add your AWS, Azure, or GCP accounts.
Grant the required read permissions so BeyondTrust can scan your environment.
Step 2: Review Cloud Permissions
Open the cloud permissions dashboard.
Look for over-provisioned accounts with unused permissions.
✓ Checkpoint: You should see a list of accounts with permission risk scores.
Step 3: Right-Size Permissions
Remove unused permissions to enforce least privilege in the cloud.
Set alerts for new over-provisioned accounts.
✅ Result: Your cloud accounts now follow least privilege with no wasted permissions.
💡 Pro Tip: Use Just-in-Time Access for cloud systems. Grant permissions only when needed and revoke them right after the task is done.
BeyondTrust Pro Tips and Shortcuts
After testing BeyondTrust for over 12 months, here are my best tips.
Keyboard Shortcuts
| Action | Shortcut |
|---|---|
| Start new support session | Ctrl + N |
| Send Ctrl+Alt+Del to remote machine | Ctrl + Shift + Del |
| Toggle full screen in remote session | Ctrl + Shift + F |
| Open file transfer window | Ctrl + Shift + T |
Hidden Features Most People Miss
- Session Recording Search: You can search audit logs by keyword, user, or date to find exactly what happened during any session.
- Canned Scripts: Save scripts in the Representative Console to run common fixes with one click during remote sessions.
- Reporting API: Export session data to your SIEM tool for automated compliance and forensic analysis.
BeyondTrust Common Mistakes to Avoid
Mistake #1: Skipping Multi-Factor Authentication
❌ Wrong: Leaving MFA disabled because it’s “too inconvenient” for admins.
✅ Right: Enable MFA or FIDO2 passwordless login for every console user from day one.
Mistake #2: Giving Everyone Full Admin Access
❌ Wrong: Making all support staff full administrators with access to every system.
✅ Right: Configure user roles so each person only accesses the systems they need.
Mistake #3: Ignoring Session Recordings
❌ Wrong: Never reviewing session recordings or audit logs after deployment.
✅ Right: Review recordings regularly and set alerts for suspicious activity in real time.
BeyondTrust Troubleshooting
Problem: Remote Session Won’t Connect
Cause: Firewall rules are blocking the connection on required ports.
Fix: Check that ports 443 and 8200 are open. Verify the Jump Client is online in the console.
Problem: Credential Injection Fails
Cause: The functional account is misconfigured or the password has expired.
Fix: Re-link the functional account in Password Safe. Verify the credentials are current.
Problem: Jump Client Shows Offline
Cause: The Jump Client service stopped or the endpoint lost network access.
Fix: Restart the BeyondTrust Jump Client service on the endpoint. Check network connectivity.
📌 Note: If none of these fix your issue, contact BeyondTrust support.
What is BeyondTrust?
BeyondTrust is a privileged access management (PAM) platform that secures who can access your most critical systems.
Think of it like a master keychain that controls every admin password and remote connection in your company.
Watch this quick overview:
It includes these key features:
- Remote Support: Connect to any device across Windows, Mac, Linux, iOS, and Android.
- Privileged Remote Access: Give vendors and admins secure, VPN-less access to critical systems.
- Endpoint Privilege Management: Remove local admin rights while still letting approved apps run.
- Password Safe: Vault, rotate, and manage all privileged credentials automatically.
- Identity Security Insights: Visualize risky privilege paths across your identity environment.
- Cloud Security: Manage permissions and enforce least privilege across AWS, Azure, and GCP.
For a full review, see our BeyondTrust review.
BeyondTrust Pricing
Here’s what BeyondTrust costs in 2026:
| Plan | Price | Best For |
|---|---|---|
| BeyondTrust Remote Support | Contact for pricing | IT support teams needing secure remote access |
| BeyondTrust Privileged Remote Access | Contact for pricing | Enterprises managing vendor and admin access |
| BeyondTrust Endpoint Privilege Management | Contact for pricing | Organizations removing local admin rights |
| BeyondTrust Password Safe | Contact for pricing | Teams vaulting and rotating privileged credentials |
Free trial: Yes — request a demo or free trial from the BeyondTrust website.
Money-back guarantee: Contact BeyondTrust sales for contract terms.
💰 Best Value: Bundle multiple products together. BeyondTrust offers discounts for multi-product and multi-year contracts.
BeyondTrust vs Alternatives
How does BeyondTrust compare? Here’s the competitive landscape:
Watch this comparison:
| Tool | Best For | Price | Rating |
|---|---|---|---|
| BeyondTrust | Enterprise PAM and remote support | Contact for pricing | ⭐ 4.4 |
| Getscreen | Budget-friendly remote access | $4.17/mo | ⭐ 3.9 |
| TeamViewer | Cross-platform remote control | $18.90/mo | ⭐ 4.4 |
| AnyDesk | Fast, lightweight connections | $32.31/mo | ⭐ 4.3 |
| Splashtop | Affordable remote desktop | $5/year | ⭐ 4.3 |
| RemotePC | Simple remote desktop for teams | $22.12/year | ⭐ 4.0 |
| RealVNC Connect | Secure on-premise remote access | $8.25/mo | ⭐ 4.4 |
| GoTo Resolve | IT management and remote support | $23/mo | ⭐ 4.3 |
| ISL Online | European-hosted remote support | $16.90/mo | ⭐ 4.0 |
Quick picks:
- Best overall: BeyondTrust — Full PAM suite with session recording and credential vaulting.
- Best budget: Getscreen — Starts at just $4.17/month for basic remote access.
- Best for beginners: Splashtop — Simple setup with plans starting at $5/year.
- Best for IT teams: GoTo Resolve — All-in-one IT management with helpdesk and RMM tools.
Looking for BeyondTrust alternatives? Here are the top options:
- 💰 Getscreen: Cheapest option at $4.17/month. Great for small teams that just need basic screen sharing and remote control.
- 🌟 TeamViewer: The most recognized name in remote access. Works across every platform with strong file transfer and collaboration tools.
- ⚡ AnyDesk: Ultra-fast connections with low latency. Ideal for designers or anyone needing smooth, real-time remote control.
- 👶 Splashtop: Easiest setup at just $5/year. Perfect for individuals and small businesses that want no-fuss remote desktop access.
- 🏢 RemotePC: Affordable annual plans for teams. Offers always-on remote access with simple deployment across multiple machines.
- 🔒 RealVNC Connect: Built on the original VNC protocol with strong security. Works great for on-premise and air-gapped environments.
- 🔧 GoTo Resolve: All-in-one IT management platform. Combines remote support, ticketing, RMM, and endpoint management in one tool.
- 🎯 ISL Online: European-hosted with strong privacy standards. Offers cloud and on-premise options for regulated industries.
For the full list, see our BeyondTrust alternatives guide.
⚔️ BeyondTrust Compared
Here’s how BeyondTrust stacks up against each competitor:
- BeyondTrust vs Getscreen: BeyondTrust wins for enterprise PAM and security. Getscreen wins on price for basic remote access needs.
- BeyondTrust vs TeamViewer: BeyondTrust offers deeper privilege management. TeamViewer is easier to set up for simple remote control.
- BeyondTrust vs AnyDesk: BeyondTrust has session recording and credential vaulting. AnyDesk is faster for lightweight one-off connections.
- BeyondTrust vs Splashtop: BeyondTrust is built for regulated enterprises. Splashtop is built for individuals and small teams on a budget.
- BeyondTrust vs RemotePC: BeyondTrust includes PAM, auditing, and compliance tools. RemotePC covers only basic remote desktop access.
- BeyondTrust vs RealVNC Connect: BeyondTrust offers a full PAM platform. RealVNC is best for simple, secure on-premise remote access.
- BeyondTrust vs GoTo Resolve: BeyondTrust focuses on privileged access security. GoTo Resolve focuses on IT service management and helpdesk.
- BeyondTrust vs ISL Online: BeyondTrust has wider PAM features. ISL Online is a strong pick for European data residency needs.
Start Using BeyondTrust Now
You learned how to use every major BeyondTrust feature:
- ✅ Remote Support
- ✅ Privileged Remote Access
- ✅ Endpoint Privilege Management
- ✅ Password Safe
- ✅ Identity Security Insights
- ✅ Cloud Security
Next step: Pick one feature and try it now.
Most people start with Remote Support.
It takes less than 5 minutes.
Frequently Asked Questions
What is BeyondTrust used for?
BeyondTrust is used for managing privileged access across IT environments. It helps organizations control who can access critical systems, vault passwords, record sessions, and provide secure remote support. Companies in finance, healthcare, and government use it to meet strict security and compliance standards.
Does BeyondTrust monitor activity?
Yes. BeyondTrust records video of every remote session and logs keystrokes. Administrators can monitor live sessions in real-time and terminate any suspicious activity. All session data is stored in searchable audit logs for compliance and forensic review.
Is BeyondTrust a VPN?
No. BeyondTrust is not a VPN. It provides VPN-less remote access using a zero-trust model. Instead of opening network tunnels, BeyondTrust creates secure, audited connections to specific systems. This is more secure because users only access what they need.
Is BeyondTrust Remote Support safe?
Yes. BeyondTrust Remote Support uses end-to-end encryption for every session. Users can see exactly what the technician does on their screen. Admins can monitor, record, and terminate sessions at any time. It was also named a Customers’ Choice in the 2024 Gartner Peer Insights report.
Who does BeyondTrust compete with?
BeyondTrust competes with CyberArk, Delinea, and One Identity in the PAM space. For remote support, competitors include TeamViewer, Splashtop, AnyDesk, and GoTo Resolve. BeyondTrust stands out by combining PAM and remote support in one platform.